 Cybersecurity
College student hacks Taiwan high-speed rail line, stopping four trains
Cybersecurity
College student hacks Taiwan high-speed rail line, stopping four trains
 Windows
Microsoft CTO confesses that 30-year-old code from the mid-90s still forms the bedrock of Windows 11
Windows
Microsoft CTO confesses that 30-year-old code from the mid-90s still forms the bedrock of Windows 11
 Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
 Cybersecurity
Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infection
Cybersecurity
Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infection
 Windows
Microsoft launches Cloud‑Initiated Driver Recovery for remote rollback of faulty updates
Windows
Microsoft launches Cloud‑Initiated Driver Recovery for remote rollback of faulty updates
 Cybersecurity
Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
Cybersecurity
Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
 Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
 Linux
CISA flags actively exploited ‘Copy Fail’ Linux kernel flaw enabling root takeover across major distros
Linux
CISA flags actively exploited ‘Copy Fail’ Linux kernel flaw enabling root takeover across major distros
 Artificial Intelligence
Anthropic's Claude Mythos isn't a sentient super-hacker, it's a sales pitch — claims of 'thousands' of severe zero-days rely on just 198 manual reviews
Artificial Intelligence
Anthropic's Claude Mythos isn't a sentient super-hacker, it's a sales pitch — claims of 'thousands' of severe zero-days rely on just 198 manual reviews
 Artificial Intelligence
Anthropic's latest AI model identifies 'thousands of zero-day vulnerabilities' in 'every major operating system and every major web browser'
Artificial Intelligence
Anthropic's latest AI model identifies 'thousands of zero-day vulnerabilities' in 'every major operating system and every major web browser'
 PC Gaming
Denuvo has been cracked in all single-player games it previously protected
PC Gaming
Denuvo has been cracked in all single-player games it previously protected
 Cybersecurity
How a cavalcade of blunders gave unauthorized users access to Claude Mythos
Cybersecurity
How a cavalcade of blunders gave unauthorized users access to Claude Mythos
 Artificial Intelligence
Anthropic's Model Context Protocol includes a critical remote code execution vulnerability
Artificial Intelligence
Anthropic's Model Context Protocol includes a critical remote code execution vulnerability
 Windows
Microsoft's April patch puts Windows domain controllers into reboot loops
Windows
Microsoft's April patch puts Windows domain controllers into reboot loops
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Contact me with news and offers from other Future brands Receive email from us on behalf of our trusted partners or sponsorsYou are now subscribed
Your newsletter sign-up was successful
Trending- TH Premium May Promo
- Where to buy AMD's 9950X3D2
- Intel Xeon 600
- RAM Combo Deals
- DLSS 5
- Bartlett Lake
- RAM Shortage
- Tech Industry
- Cybersecurity
Microsoft BitLocker-protected drives can now be opened with just some files on a USB stick — YellowKey zero-day exploit demonstrates an apparent backdoor
Also, it's a twofer with the GreenPlasma zero-day local privilege escalation.
When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.

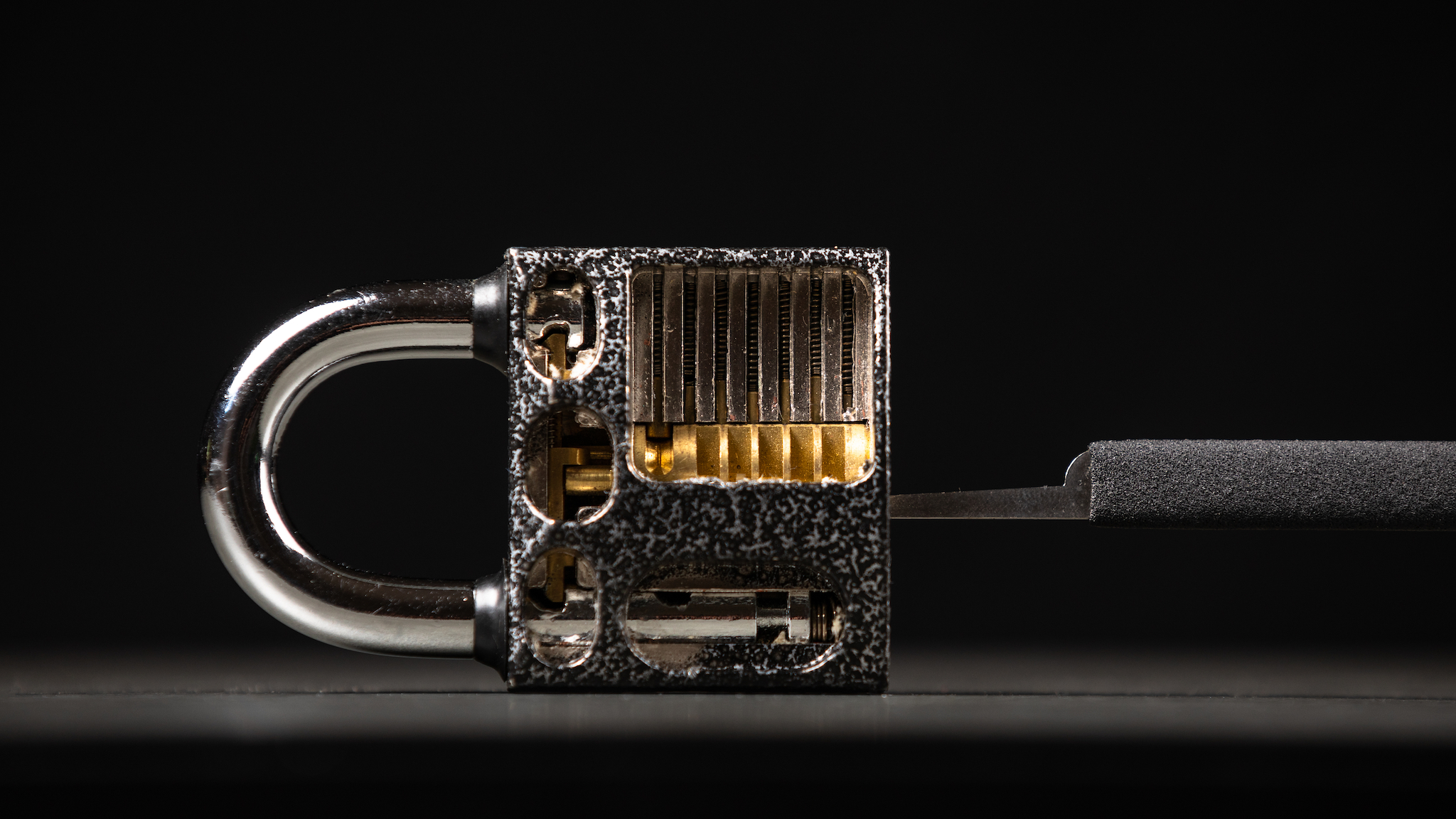
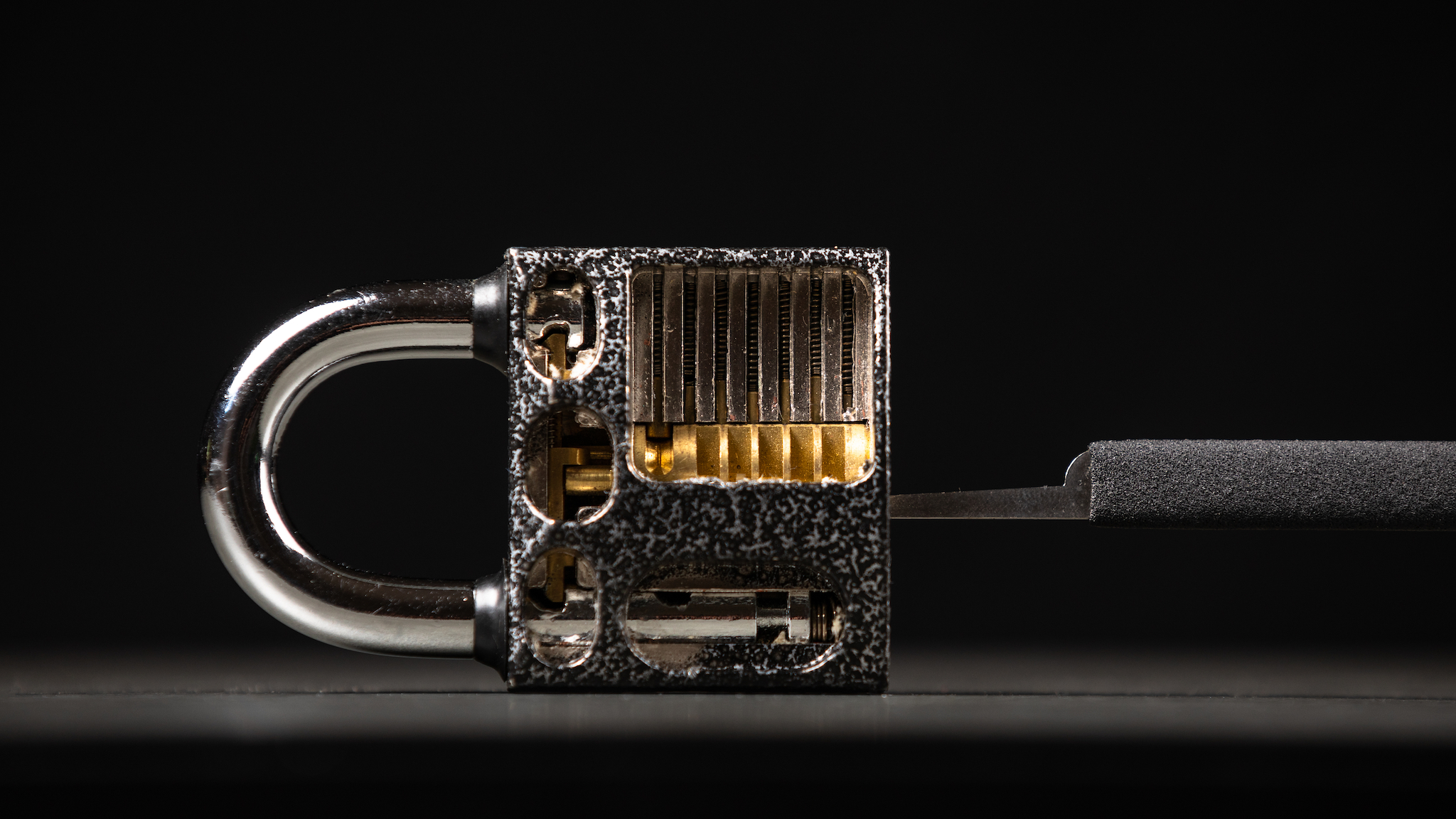
There's nothing more dangerous than a bored engineer with a screwdriver, and hell hath no fury like a security researcher scorned. Last month, Security researcher Chaotic Eclipse (aka Nightmare-Eclipse) published two zero-day exploits, BlueHammer and RedSun, that made Windows Defender offer up system administrator privileges. They did this after their disclosure reports were allegedly dismissed by Microsoft's security team, resulting in a vendetta of sorts. Eclipse has now done it again, posting two new zero-day exploits, the first one an extremely serious BitLocker exploit named Yellow Key that grants full access to a locked drive. The second one, GreenPlasma, doesn't have a complete proof-of-concept (PoC), but it allegedly performs a local privilege escalation and gains system-level access. Given Eclipse's track record, it's a fair bet that it works as advertised.
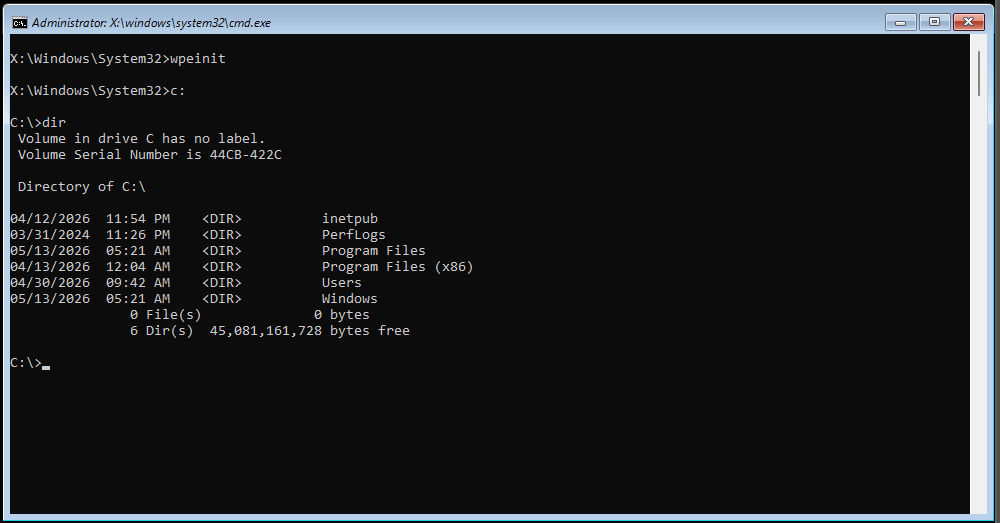
YellowKey can be triggered simply by merely copying some files to a USB stick and rebooting to the Windows Recovery Environment. We tested this ourselves, and sure enough, not only does it work, it bears all the hallmarks of a backdoor, down to the exploit's files disappearing from the USB stick after it's used once.
The process is dead simple: grab any USB stick, get write access to the "System Volume Information," and copy into it the "FsTx" folder and its contents. Shift+click Restart to get Windows to the recovery environment, but then switch to holding down the Control key and don't let go. The machine will reboot, and without asking any questions or showing any menus, will drop you in an elevated command line with full access to the formerly Bitlocked drive, without asking for any keys.
Latest Videos From
 You may like
You may like
-
 Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
-
 New 'GeForge' and 'GDDRHammer' attacks can fully infiltrate your system through Nvidia's GPU memory
New 'GeForge' and 'GDDRHammer' attacks can fully infiltrate your system through Nvidia's GPU memory
-
 Zombie ZIP vulnerability lets malware stroll past gates of 95% of AV suites
Zombie ZIP vulnerability lets malware stroll past gates of 95% of AV suites
To say that this is dangerous is an understatement. Not only is it an immediate concern as BitLocker cannot be trusted for encrypting drives, but the way the exploit executes and its files disappear also raises very uncomfortable corporate and/or political questions. YellowKey also reportedly works in Windows Server 2022 and 2025, but not in Windows 10.
BitLocker protects millions of machines worldwide across home, enterprises, and governments, especially as it's enabled by default in Windows 11. As far as we can tell, a drive can't be taken from machine Alice and opened in machine Bob because the encryption keys are in Alice's TPM, but it's not hard to just up and steal a laptop, mini-PC, or even desktop.
Eclipse notes that using a full TPM-and-PIN setup doesn't help, as apparently, they have a variant for that scenario that they haven't published a PoC for. They also state the vulnerability is well-hidden, and that they "could have made some insane cash selling this, but no amount of money will stand between me and my determination against Microsoft."
As for GreenPlasma, it's supposed to get an attacker full system-level access (even higher than administrator) by manipulating the CTFMon process into placing a crafted memory section object — a slice of memory that can be shared between processes or mapped to a file — in any Windows' Object Manager section the SYSTEM user has write access to, bypassing regular access controls.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Contact me with news and offers from other Future brandsReceive email from us on behalf of our trusted partners or sponsorsBy submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.From thereon, the exploit code can get access to regions of memory they're not meant to and leverage that for any number of shenanigans, the most obvious one being getting full system access. This is bad enough for a desktop system, as any program can get full access, but it's particularly bad for server environments, where any regular user can get control of the server and, by extension, everyone else's data.
Meanwhile, as of this writing, there is no official response from the company about YellowKey or GreenPlasma. BlueHammer has already been patched, and Chaotic claims that Microsoft silently patched RedSun, but there's no official word on that either.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.
See all comments (30) Social Links NavigationContributorBruno Ferreira is a contributing writer for Tom's Hardware. He has decades of experience with PC hardware and assorted sundries, alongside a career as a developer. He's obsessed with detail and has a tendency to ramble on the topics he loves. When not doing that, he's usually playing games, or at live music shows and festivals.
 Cybersecurity
Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
Cybersecurity
Zero-day exploit instantly grants administrator access on most Linux distributions since 2017
 GPUs
New 'GeForge' and 'GDDRHammer' attacks can fully infiltrate your system through Nvidia's GPU memory
GPUs
New 'GeForge' and 'GDDRHammer' attacks can fully infiltrate your system through Nvidia's GPU memory
 Cybersecurity
Zombie ZIP vulnerability lets malware stroll past gates of 95% of AV suites
Cybersecurity
Zombie ZIP vulnerability lets malware stroll past gates of 95% of AV suites
 Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
 Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
 Cybersecurity
Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning given
Cybersecurity
Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning given
 Cybersecurity
Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infection
Cybersecurity
Compromised Mistral AI and TanStack packages may have exposed GitHub, cloud and CI/CD credentials in 'mini Shai Hulud' malware infection
 Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
Cybersecurity
Google cybersecurity boffins found at least one AI-developed zero-day exploit
 Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
Cybersecurity
90-day vulnerability disclosure may be dead due to AI, leaving systems exposed to zero-day attacks
 Cybersecurity
Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning given
Cybersecurity
Dirty Frag exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning given
 Cybersecurity
College student hacks Taiwan high-speed rail line, stopping four trains
Cybersecurity
College student hacks Taiwan high-speed rail line, stopping four trains
 Cybersecurity
Google Chrome 'silently' downloads 4GB AI model to your device without permission, report claims
Cybersecurity
Google Chrome 'silently' downloads 4GB AI model to your device without permission, report claims
 Windows
Microsoft launches Cloud‑Initiated Driver Recovery for remote rollback of faulty updates
Windows
Microsoft launches Cloud‑Initiated Driver Recovery for remote rollback of faulty updates
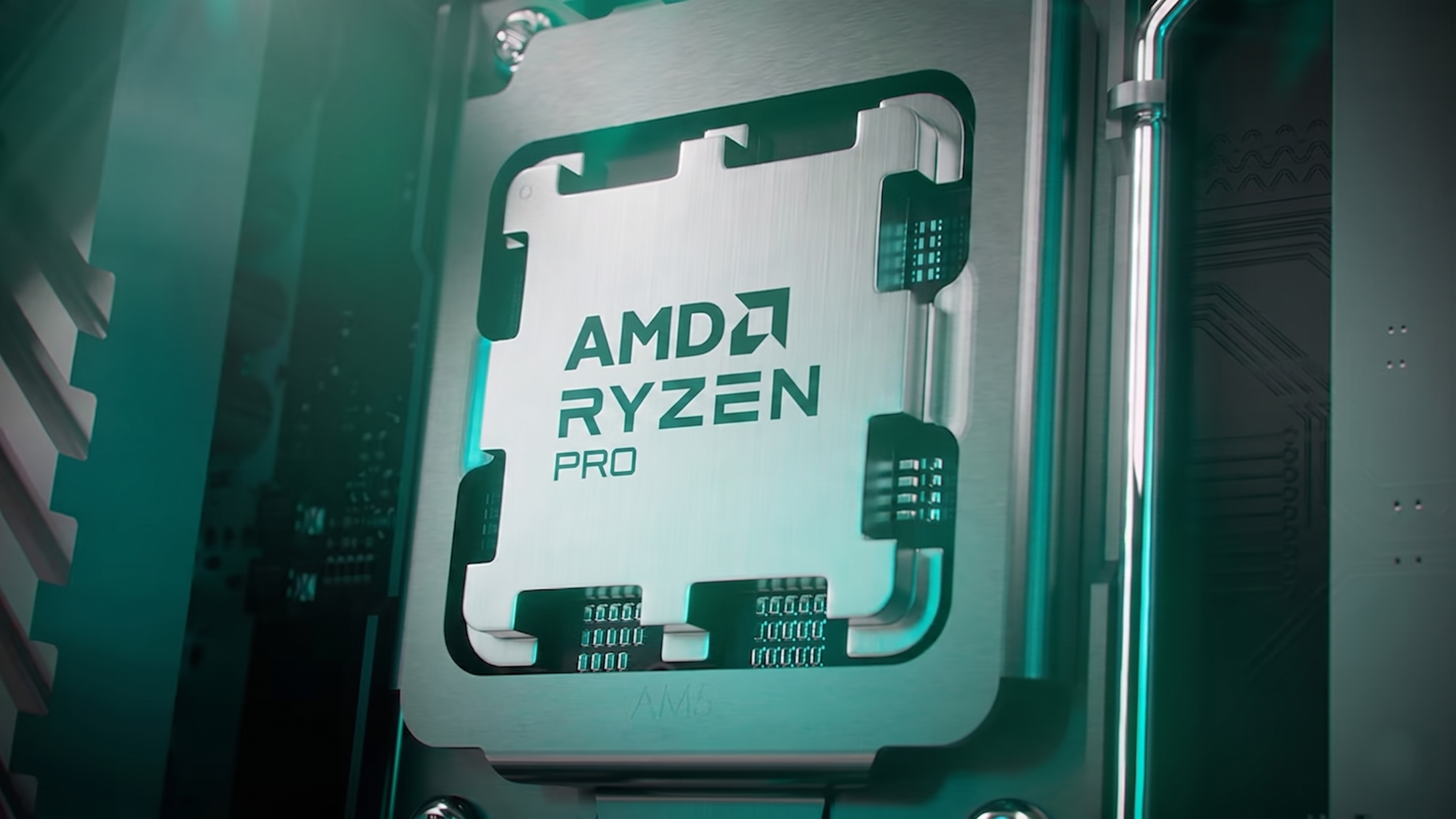 CPUs
AMD expands its Ryzen 9000 PRO lineup with six new SKUs, now featuring 3D V-Cache for the first time
CPUs
AMD expands its Ryzen 9000 PRO lineup with six new SKUs, now featuring 3D V-Cache for the first time
 Tech Industry
Samsung's critical union negotiations break down eight days before planned 18-day chip factory strike that's projected to cost $700 million per day
Tech Industry
Samsung's critical union negotiations break down eight days before planned 18-day chip factory strike that's projected to cost $700 million per day
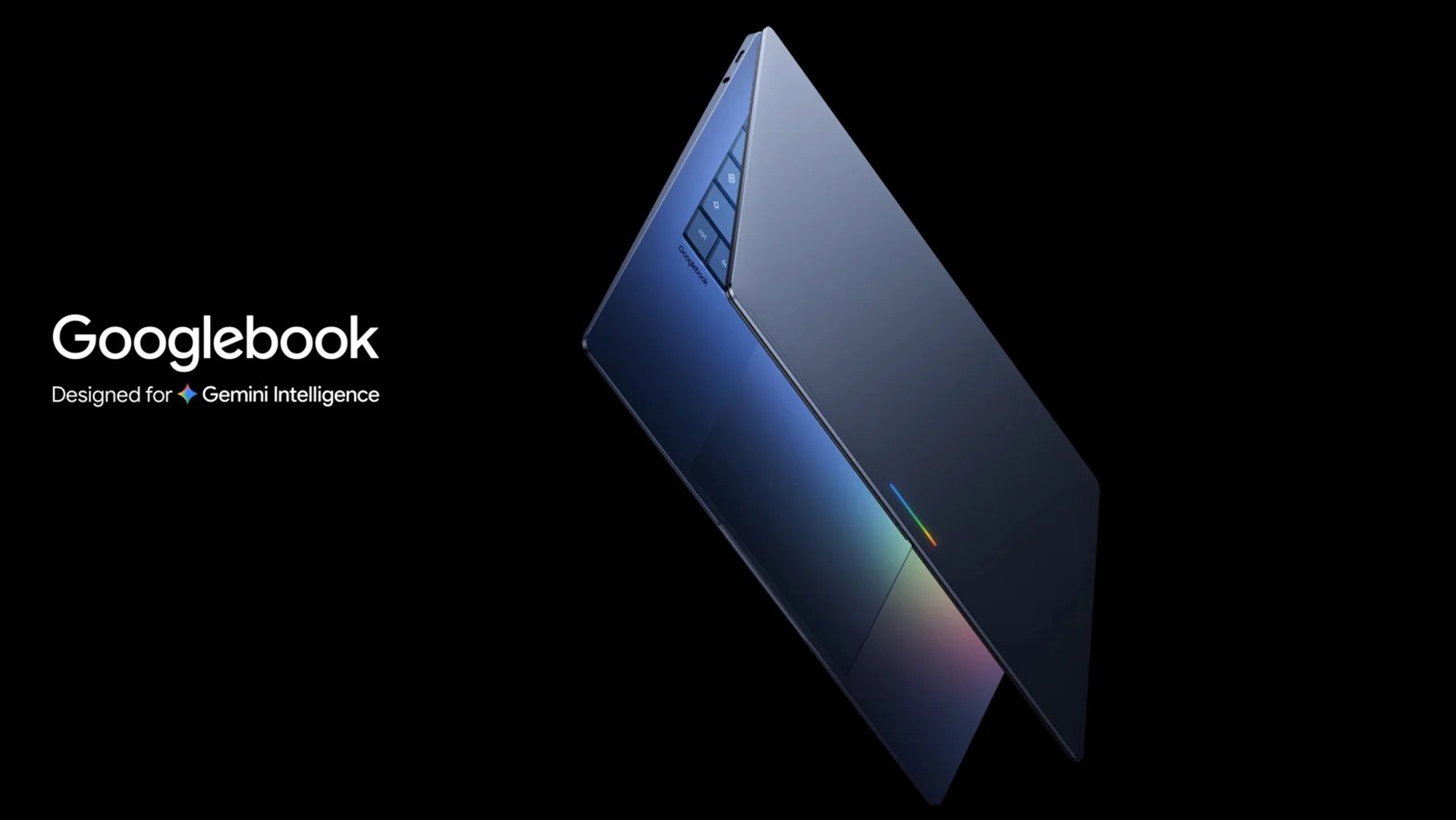 Laptops
Intel, Qualcomm confirm Googlebook AI laptop partnership, opening x86 and ARM possibilities for new OS
Laptops
Intel, Qualcomm confirm Googlebook AI laptop partnership, opening x86 and ARM possibilities for new OS
 SSDs
SSD prices skyrocket by 300% in Japan, bringing 8TB Samsung 9100 drive to an eye-watering $3,500
SSDs
SSD prices skyrocket by 300% in Japan, bringing 8TB Samsung 9100 drive to an eye-watering $3,500
 Artificial Intelligence
Google is reportedly in talks with SpaceX to launch its orbital data centers
Artificial Intelligence
Google is reportedly in talks with SpaceX to launch its orbital data centers
- ezst036 Reply
- Gururu Reply
- -Fran- Reply
- dwd999 Reply
- S58_is_the_goat Reply
- TechieTwo Reply
- Dr3ams SOS, DD it's Microsucks. What did you expect? :anguished:yawn... Reply
-
USAFRet
SOS, DD it's Microsucks. What did you expect? :anguished:And yesterday it was Apple, and last week it was Linux.
Your point? Reply -
ezst036
You're telling me the most relevant reason of why Microsoft forced everyone to have (enabled) TPM in order to install and use Win11You know that actually is a really good point Fran.
We all know the TPM security propaganda since the Windows 11 launch. However why are TPM chips necessary in practice if they don't actually secure? Reply -
-Fran-
You know that actually is a really good point Fran.
We all know the TPM security propaganda since the Windows 11 launch. However why are TPM chips necessary in practice if they don't actually secure?They are not necessary. That is the grift.
Encryption (reliable even) has existed for ages in different ways and shapes before TPM was designed and implemented. It's a nice to have, for sure, but make it mandatory? Nah.
Marrying your hardware to a physical encryption tool does not make it inheritely more secure. That's just gaslighting: "it's ok, this is totally to make your stuff more secure! pinky promise!". It's been widely reported that MS doesn't even use anything with TPM unless you actively enable BitLocker or anything else that requires encryption and supports TPM.
But oh well... TPM is not a bad thing, just to be clear. Microsoft forcing people to have it for an OS upgrade is the bad thing.
Regards. Reply - View All 30 Comments